Design and Evaluation of a High-Availability Secure Mail Relay with OAuth2 Authentication for Legacy Systems
DOI:
https://doi.org/10.65205/jcct.2026.e2971Keywords:
Secure Mail Relay, Legacy Applications, Modern Authentication, OAuth2 Agent, Service-Level High AvailabilityAbstract
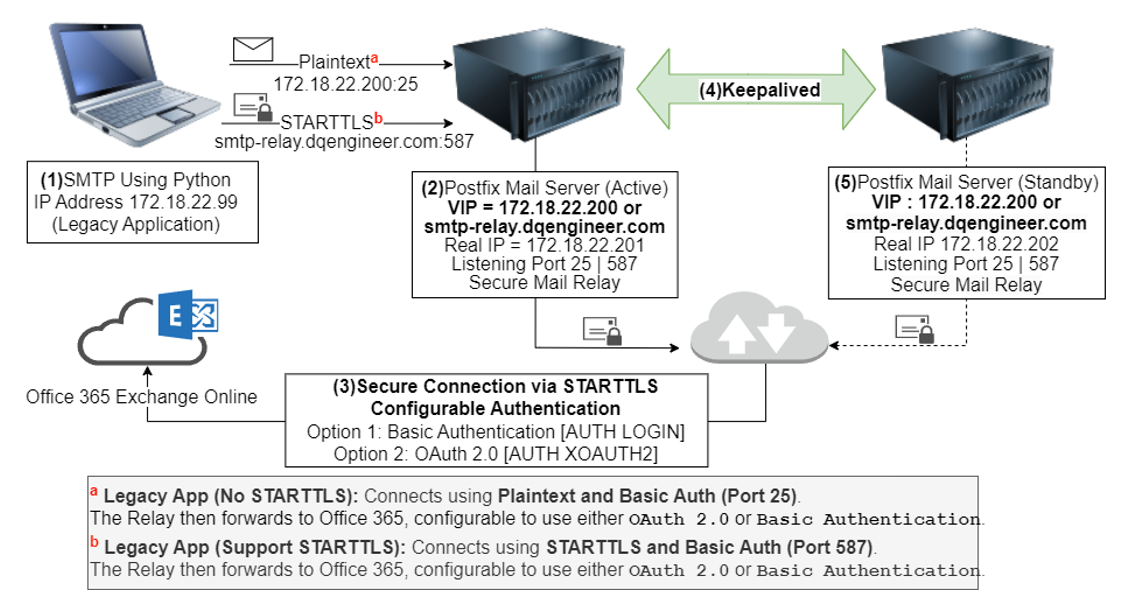
In an era of escalating cyber threats, the enforcement of Modern Authentication (OAuth 2.0) by Microsoft 365 has created a critical compatibility gap for legacy applications that cannot be modified, posing significant risks to data security and business continuity, particularly in email communication systems. This research proposes High-Availability Secure Mail Relay architecture. The core novelty lies in the development of an “OAuth2 Agent Module” an intermediary mechanism designed to seamlessly translate legacy authentication protocols into OAuth 2.0 standards without requiring source code modifications. This is integrated with a Service-Level High Availability (HA) system capable of detecting internal service failures. Experimental results confirm that (1) The proposed architecture achieves a 100% success rate in relaying emails using OAuth 2.0 standards (2) While the enhanced security processing introduces a slight latency increase to 2.158 seconds compared to traditional Basic Authentication 1.908 seconds, performance remains within acceptable limits and (3) The HA mechanism successfully executes service failover in an average of 1.312 seconds. This study contributes a practical framework for retrofitting legacy systems to comply with modern security mandates while ensuring resilience.
Downloads
References
Cassen, A., & Contributors. (2017). Keepalived User Guide (Release 1.2.15). The Keepalived Project. https://keepalived.readthedocs.io/_/downloads/en/stable/pdf/
Chatterjee, N., Majumdar, S., Das, P. P., & Chakrabarti, A. (2024). Tool Assisted Agile Approach for Legacy Application Migration. Research Square. https://doi.org/10.21203/rs.3.rs-3323311/v1 DOI: https://doi.org/10.21203/rs.3.rs-3323311/v1
Cryptography. (2023). Welcome to Pyca/Cryptography (Version 41.0.7) [Computer Software]. Cryptography. https://cryptography.io/en/41.0.7 DOI: https://doi.org/10.3390/cryptography7030041
Dovecot Team. (n.d.). Postfix and Dovecot SASL. Dovecot. https://doc.dovecot.org/2.3/configuration_manual/howto/postfix_and_dovecot_sasl/#howto-postfix-and-dovecot-sasl
Faseeha, U., Jamil Syed, H., Samad, F., Zehra, S., & Ahmed, H. (2025). Observability in Microservices: An In-Depth Exploration of Frameworks, Challenges, and Deployment Paradigms. IEEE Access, 13, 72011-72039. https://doi.org/10.1109/ACCESS.2025.3562125 DOI: https://doi.org/10.1109/ACCESS.2025.3562125
Gbenle, T. P., Abayomi, A. A., Uzoka, A. C., Ogeawuchi, J. C., Adanigbo, O. S., & Odofin, O. T. (2022). Applying OAuth2 and JWT Protocols in Securing Distributed API Gateways: Best Practices and Case Review. International Journal of Multidisciplinary Research and Growth Evaluation, 3(5), 628-634. https://doi.org/10.54660/.IJMRGE.2022.3.5.628-634 DOI: https://doi.org/10.54660/.IJMRGE.2022.3.5.628-634
Hardt, D. (2012). The OAuth 2.0 Authorization Framework (No. RFC6749). Internet Engineering Task Force. https://doi.org/10.17487/rfc6749 DOI: https://doi.org/10.17487/rfc6749
Hoffman, P. (2002). SMTP Service Extension for Secure SMTP over Transport Layer Security (No. RFC3207). Internet Engineering Task Force. https://doi.org/10.17487/rfc3207 DOI: https://doi.org/10.17487/rfc3207
Klensin, J. (2008). Simple Mail Transfer Protocol (No. RFC5321). Internet Engineering Task Force. https://doi.org/10.17487/rfc5321 DOI: https://doi.org/10.17487/rfc5321
Matcha, S., & Kumar, M. (2025). Enhancing Software Security with OAuth 2.0: Implementation Strategies and Vulnerability Mitigation. Journal of Emerging Technologies and Innovative Research, 12(3), e886–e902.
Microsoft. (2025a). Microsoft Identity Platform and OAuth 2.0 Client Credentials Flow. Microsoft Learn. https://learn.microsoft.com/en-us/entra/identity-platform/v2-oauth2-client-creds-grant-flow
Microsoft. (2025b). Microsoft Authentication Library (MSAL) for Python. Microsoft Learn. https://learn.microsoft.com/en-us/entra/msal/python
Mishra, A. (2020). Legacy System Modernization: Effective Strategies and Best Practices. International Journal of Leading Research Publication, 1(3), 1-7. https://doi.org/10.5281/zenodo.14769544
Oliveira, P. M., Vieira, M. B., Ferreira, I. C., Leite, J. P. R. R., Oliveira, E. M., Kuehne, B. T., Moreira, E. M., & Carpinteiro, O. A. S. (2022). ABL: An Original Active Blacklist Based on a Modification of the SMTP. arXiv. https://doi.org/10.48550/arXiv.2208.10602
Postfix. (n.d.). Postfix Architecture Overview. https://www.postfix.org/OVERVIEW.html
Putranto, E. A. (2019). High Availability Server Implementation Using NGINX, Keepalived, and Varnish to Ease Web Server Access. ResearchGate. https://www.researchgate.net/publication/334451751
Python Software Foundation. (2025). smtplib - SMTP Protocol Client. https://docs.python.org/3.12/library/smtplib.html#module-smtplib
Sharabov, M., Tsochev, G., Gancheva, V., & Tasheva, A. (2024). Filtering and Detection of Real-Time Spam Mail Based on a Bayesian Approach in University Networks. Electronics, 13(2), 374. https://doi.org/10.3390/electronics13020374 DOI: https://doi.org/10.3390/electronics13020374
The aiosmtpd Developers. (2025). The SMTP Module. Read the Docs. Python. https://aiosmtpd.aio-libs.org/en/latest/smtp.html
The Exchange Team. (2024). Exchange Online to Retire Basic Auth for Client Submission (SMTP AUTH). Microsoft Community Hub. https://techcommunity.microsoft.com/blog/exchange/exchange-online-to-retire-basic-auth-for-client-submission-smtp-auth/4114750
Downloads
Published
How to Cite
Issue
Section
Categories
License
Copyright (c) 2026 Journal of Computer and Creative Technology

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.